We regret to inform you that the CannyApp holiday prepaid debit card scheme is now closed.
If you already have a CannyApp card and account, you can link to the formal notice HERE which will explain the process from hereonin.
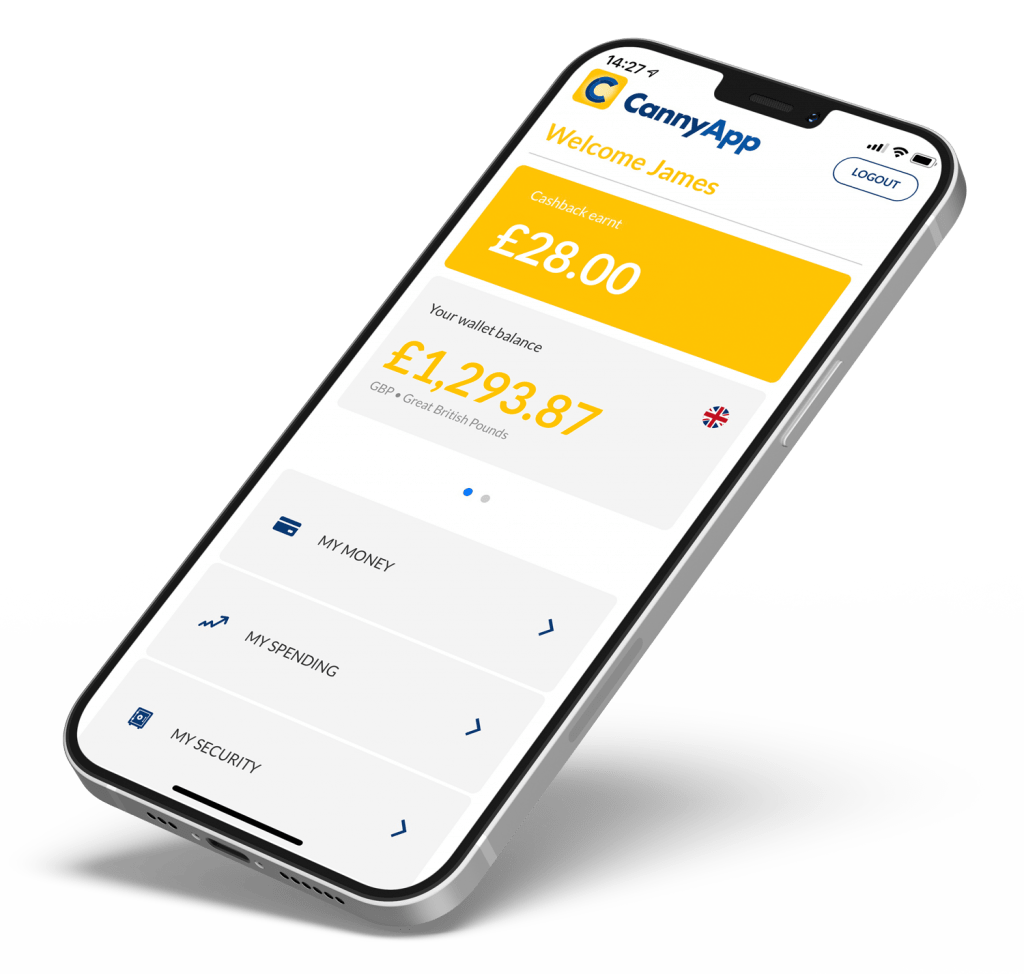
Your monies and Cashback accrued to date is SAFE AND PROTECTED. If you wish to redeem your funds before 21st November 2023, please contact us by email at support@cannyapp.co.uk.
After the 21st November, redemptions will be managed by Lerex Technology who can be contacted at support@lerextech.com.